Zimperium is proud to be the global leader in enterprise mobile security. While many of our detection and architectural innovations have come from the efforts of our incredible mobile security experts, others are the result of following one time-tested rule: listening to our customers. One thing customers have consistently told […]
zLabs at HITB Singapore: The Road to iOS Sandbox Escape
This week at HITB Singapore, Zimperium zLabs’ security researcher, Rani Idan (@raniXCH), is conducting a session titled “The Road to iOS Sandbox Escape.” Rani’s fellow zLab’s researcher, Adam Donenfeld (@doadam), is also conducting a session titled “Viewer Discretion Advised: (De)coding an iOS Vulnerability.” Here is the abstract for Rani’s session. We will post the recording of the session […]
zLabs at HITB Singapore: (De)coding an iOS Vulnerability
This week at HITB Singapore, Zimperium zLabs’ security researcher, Adam Donenfeld (@doadam) is conducting a session titled “Viewer Discretion Advised: (De)coding an iOS Vulnerability.” Another zLabs researcher, Rani Idan (@raniXCH), is also doing a session titled “The Road to iOS Sandbox Escape.” Here is the abstract for Adam’s session. We will post the recording of the session when it […]
ZipperDown Vulnerability: 100 Million iOS Users (Not Using Zimperium) at Risk of Exploit
Last Monday, security researchers from iOS jailbreak firm, Pangu Lab, announced a vulnerability that they believe affects around 10% of all iOS apps. In a blog on its newly created information site, https://zipperdown.org/ , Pangu stated that its researchers noticed “a common programming error, which leads to severe consequences such […]
ziVA: Zimperium’s iOS Video Audio Kernel Exploit
Follow @doadam Following my previous post, I’m releasing ziVA: a fully chained iOS kernel exploit that (should) work on all the iOS devices running iOS 10.3.1 or earlier. The exploit itself consists of multiple vulnerabilities that were discovered all in the same module: AppleAVEDriver. The exploit will be covered in […]
ZPI: One approach to rule them all
In 1975, a book was published that changed the way we approach complex problems. Inspired on how nature works “Adaptation in Natural and Artificial Systems” set the bases of genetic algorithms. The release date of this blogpost is strongly linked to that book, it is a symbolic tribute to its […]
Jailbreak versus Compromise…
We see a lot of confusion in the market about precisely what it means to jailbreak a device–and that confusion could lead to serious problems, especially regarding a hacker performing a jailbreak to attack a device. The security industry is notoriously full of acronyms, buzzwords and generally opaque jargon. Here at […]
Zimperium zLabs iOS Security Advisories
As part of zLab’s platform research team, I’ve tried to investigate an area of the kernel that wasn’t thoroughly researched before. After digging into some of Apple’s closed-source kernel modules, one code chunk led to another and I’ve noticed a little-known module, which I’ve never seen before, called AppleAVE. AppleAVE was written neglecting basic security […]
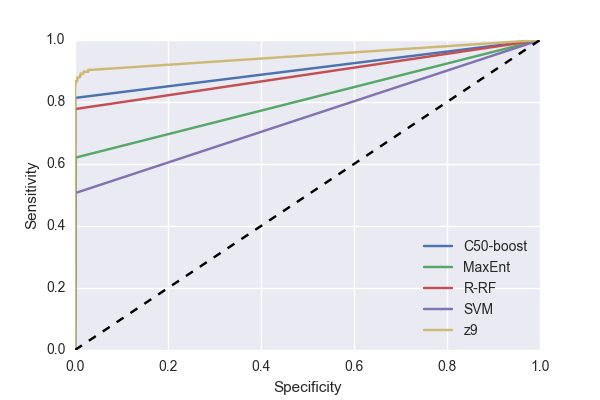
Zero Packet Inspection
Introduction In this blogpost I describe the history of z9, our detection engine. I will show its performance over reference data sets commonly used in the machine learning community. I’ll then describe how we apply it to detect networks attacks without any type of packet inspection. Eventually, we encourage you to participate by helping […]
NDAY-2017-0101: iCloud Information Leak
By: Zuk Avraham Follow Zuk Avraham (@ihackbanme) Nicolas Trippar Follow Nicolas Trippar (@ntrippar) zNID: NDAY-2017-0101 CVE: Unknown Type: Information Disclosure Platform: iOS < 10.3 Device type: iPhone, iPod iOS bulletin: https://support.apple.com/en-us/HT207617 Public release date: 25th of May, 2017 Credit: Anonymous Download Exploit (password zimperium_ndays) Vulnerability Details An XPC service com.apple.coreservices.appleid.authentication can be accessed […]
Mobile Security Updates
Recent Posts
- What Good Mobile App Security Visibility Looks Like: Discover What Lurks Within Your Enterprise’s Mobile Ecosystem
- Zimperium Positioned as the Leader in the 2024 SPARK MatrixTM for In-App Protection by Quadrant Knowledge Solutions
- Understanding IRAP: Australia’s Commitment to Upholding Best-in-Class Security Standards