Zimperium would like to congratulate Brom Stibitz and Laura Clark from Michigan for winning the 2021 StateScoop 50 Awards. StateScoop 50 Awards honor the most innovative and influential projects in state government and the people with the passion and drive to advance the use of digital technology inside state agencies. […]
Zimperium and Google Partner to Fight Bad Apps through App Defense Alliance
We are thrilled to announce Google has selected us to help ensure the safety of the millions of apps in the Google Play Store through its App Defense Alliance. As a member of the App Defense Alliance, Google will provide us access to mobile apps as they are being queued […]
Malicious Websites Put iOS Devices At Risk
In an excellent and deep blog analysis, Ian Beer of Google’s Project Zero outlines five separate iOS exploit chains that were found on a small collection of hacked websites. The hacked sites were being used in indiscriminate watering hole attacks against their visitors, using iOS 0-day. (For another watering hole […]
To Be…Protected, or not To Be…Protected. That is the Question.
These last few days could have CIOs and CISOs very nervous. Two news stories about mobile devices pose real threats for enterprises around the world: From Forbes, “millions of shiny new Android smartphones are being purchased with dangerous malware factory-installed, according to Google’s own security research team.” Also from Forbes, […]
Latest Android Malware is Not a Surprise; Zimperium Customers Protected
According to news reports, a new strain of Android malware has infected 25 million devices and modified legitimate apps with a malicious ads module. It’s believed the malware originated from a Chinese internet company that helps Chinese Android developers publish and promote their apps in foreign markets. The malware was […]
Zimperium Webinar Series: Seven Deadly (Mobile Security) Sins… According to CISOs
Zimperium, a global leader in enterprise mobile threat defense (MTD) and a leading provider of real-time, on-device protection against known and unknown mobile threats, hosted a series of webinars focusing on seven of the problem areas, or deadly sins, chief information security officers (CISOs) must address. Most organizations now realize that mobile […]
Malicious WiFi Connections: Welcome to RSA Conference 2019
Nicolás Chiaraviglio (@chiconara) We recently blogged about attacks perpetrated at WiFi networks in Barcelona before and during the 2019 Mobile World Congress (MWC). We found an astonishing amount: estimating more than 7,000 threats in less than four days. Furthermore, 25 percent of those threats were detected in hotels, and of those, 70 percent […]
Machine Learning vs Signatures, Round N: Once Again, Zimperium Detects Malware No One Else Does
Analysis & Post By: Alex Calleja (@alximw) Matteo Favaro (@fvrmatteo) Advertising and click fraud campaigns are one of the most common mobile malware-based monetization techniques. Although they are considered a lawful income source in most app markets, they can put the user’s privacy at risk and even cause economic damage. Once […]
Your App, Our Security: Zimperium Launches Latest Version of Machine Learning-Based Security for Mobile Apps
Zimperium is announcing the availability of the latest version of zIAP, our industry-leading, machine learning-based mobile security solution developed specifically to embed into existing mobile apps. Organizations who build mobile apps frequently struggle with how to successfully meet the critical need to protect sensitive data, reduce fraud and ensure security […]
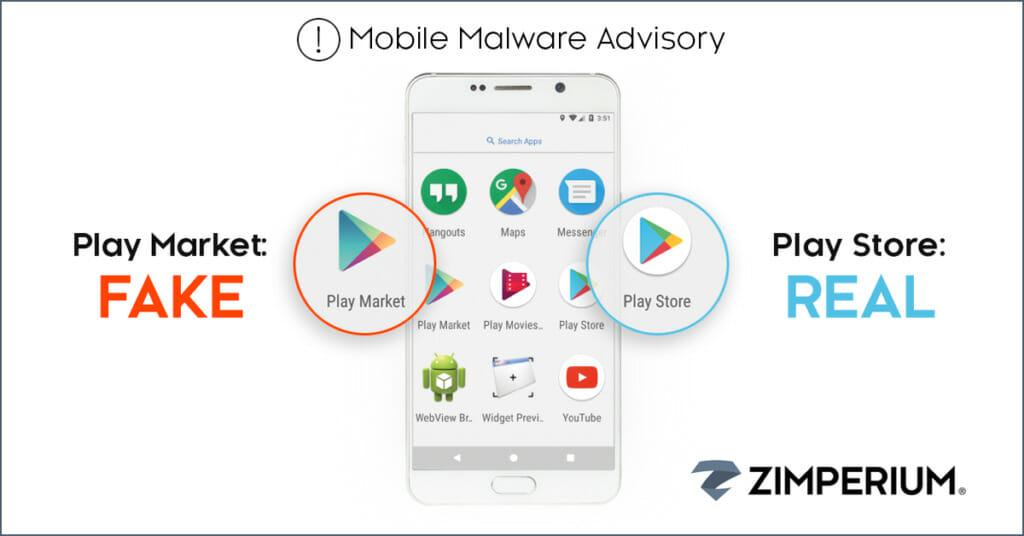
Fake Play Market: Zimperium’s z9 against Social Engineering Attack Vectors
Analysis & Post By: Alex Calleja (@alximw) Matteo Favaro (@fvrmatteo) Introduction Since the beginning of 2018, researchers in Zimperium’s zLabs have been tracking a rise in the frequency and sophistication of applications that have been loaded outside of the official Google Play Store. Many of these have leveraged social engineering techniques […]