The Hacker News recently published a story that discussed a joint communication among the German intelligence apparatus, the Federal Office for the Protection of the Constitution (BfV), and South Korea’s National Intelligence Service (NIS), warning readers about new tactics used by a North Korean threat actor called Kimsuky. Learn more about Kimsuky and how Zimperium Mobile Threat Defense (MTD) customers are protected against these threats.
2022 Recap: The Top Mobile Security Stories from Last Year
Over the course of 2022, a number of significant mobile security stories emerged. These events had a big impact last year, and they will certainly shape the security landscape that we must navigate as we enter 2023. Here is our take on the top mobile security stories that emerged in 2022.
MoneyMonger: Predatory Loan Scam Campaigns Move to Flutter
The Zimperium zLabs team recently discovered a Flutter application with malicious code. The Flutter-obfuscated malware campaign, MoneyMonger, is solely distributed through third-party app stores and sideloaded onto the victim’s Android device and most commonly take advantage of social engineering through phishing messages, compromised websites, rogue WiFi networks, and social media to distribute the download links. Read more to learn how Zimperium customers are protected.
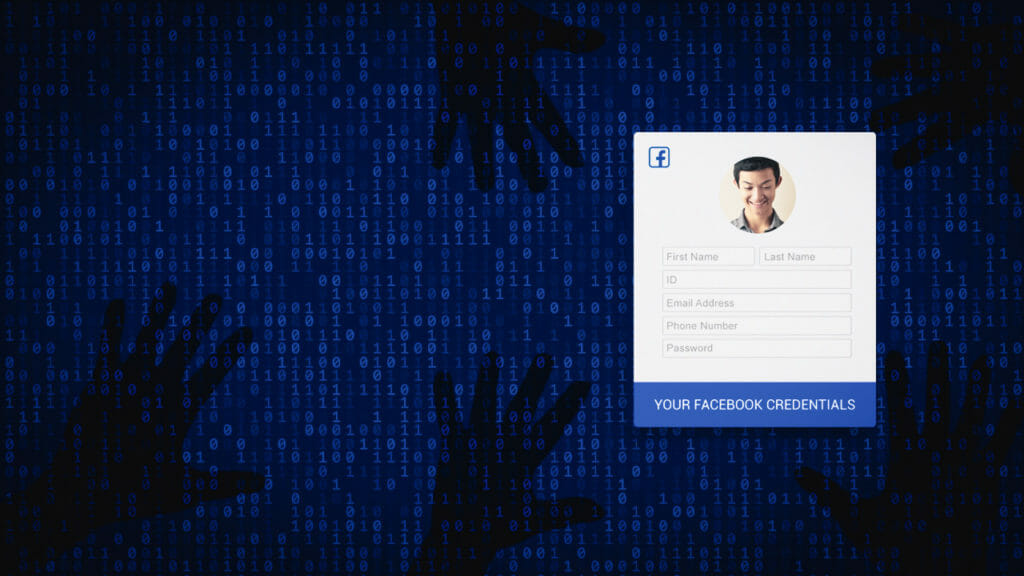
Schoolyard Bully Trojan Facebook Credential Stealer
Zimperium zLabs has discovered a new Android threat campaign, the Schoolyard Bully Trojan, which has been active since 2018 and has spread to over 300,000 victims and is specifically targeting Facebook credentials. To learn more about this new threat, read more on our blog.
The Case of Cloud9 Chrome Botnet
The Zimperium zLabs team recently discovered a malicious browser extension, originally called Cloud9, which not only steals the information available during the browser session but can also install malware on a user’s device and subsequently assume control of the entire device. In this blog, we will take a deeper look into this malicious browser extension. Read more.
4 Common types of Malware and What’s the Difference (Trojan, Spyware, Viruses, Ransomware)
Malware is malicious code that threat actors use to compromise data collected, stored, processed, or transmitted by mobile devices, computers, servers, or any other internet-connected device or application. As part of an organization’s security and data protection program, it should have a plan in place that, at minimum, mitigates risk […]
Half-Year Review: Emerging Mobile Threats and Key Trends in 2022
As the saying goes, time is money. While this does remain true, I’d also argue data is money. The mobile phones we carry in our pockets have quickly come to represent our personal ATMs. We use our phones to make purchases, send money, and do banking. On the same note, […]
ABCsoup: The Malicious Adware Extension with 350 Variants
What can ABCsoup do? Recently Zimperium discovered and began monitoring the growth of a wide range of malicious browser extensions with the same extension ID as that of Google Translate, deceiving users into believing that they have installed a legitimate extension. Similar to app spoofing and cloning, these malicious applications […]
The State of Browser Extension Malware
It is time for us to change how we think about malware. No longer is it limited to one specific operating system or device type. Like with phishing attacks, malware developers have been working on malware that can impact a broader range of systems to increase the number of potential […]
Financially Motivated Mobile Scamware Exceeds 100M Installations
Research by Aazim Bill SE Yaswant and Nipun Gupta While some financially motivated scams may seem simple on the surface, the truth of the matter is that cybercriminals are investing large amounts of money into strategies and infrastructure to scale up their malicious campaigns. Those investments are paying off as […]
Mobile Security Updates
Recent Posts
- What Good Mobile App Security Visibility Looks Like: Discover What Lurks Within Your Enterprise’s Mobile Ecosystem
- Zimperium Positioned as the Leader in the 2024 SPARK MatrixTM for In-App Protection by Quadrant Knowledge Solutions
- Understanding IRAP: Australia’s Commitment to Upholding Best-in-Class Security Standards