The rising threats against government agencies are an ongoing concern in today’s threat landscape. With nation-state actors targeting local, state, and federal agencies, security teams in the government sector that leverage Microsoft’s Azure Government ecosystem are realizing they need more robust security and threat intelligence to secure government-issued and BYO […]
Zimperium Joins NIST Project on Zero Trust Architectures
Zimperium has been working closely with the National Cybersecurity Center of Excellence (NCCoE) at the National Institute of Standards and Technology (NIST). The NCCoE is a collaborative hub in which industry organizations, government agencies, and academic institutions work together to address businesses’ most pressing cybersecurity challenges. Through these engagements, we […]
Mobile Threat Defense for OMB Memorandum M-22-09
OMB Memorandum M-22-09: Moving the U.S. Government Toward Zero Trust Cybersecurity Principles. On January 26, 2022, the Office of Management and Budget (OMB) published M-22-09 Moving the U.S. Government Toward Zero Trust Cybersecurity Principles. M-22-09 sets out activities that agencies need to undertake to meet the requirements under Executive Order […]
2022 Predictions: 5 Mobile Threats to Look for This Year
Recent years have made abundantly clear that attempting to predict what’s to come in the future can be a pretty dicey proposition. However, it is also true that current trends can paint a clear picture of how we can expect things to unfold. This is very true in cyber security, […]
Financially Motivated Mobile Scamware Exceeds 100M Installations
Research by Aazim Bill SE Yaswant and Nipun Gupta While some financially motivated scams may seem simple on the surface, the truth of the matter is that cybercriminals are investing large amounts of money into strategies and infrastructure to scale up their malicious campaigns. Those investments are paying off as […]
Pegasus Spyware Found on U.S. State Department iPhones
On December 3rd, Christopher Bing and Joseph Menn at Reuters disclosed that iPhones of numerous U.S. State Department employees were hacked by an unknown assailant using Pegasus spyware developed by the Israel-based NSO Group. While it may be easy to dismiss this as a geopolitical or nation-state incident, it would […]
Q&A with CISA’s Jen Easterly: Every Part Of Our Interconnected Ecosystem Needs Securing, Including Mobile
Jen Easterly, the new Director of the Cybersecurity & Infrastructure Security Agency CISA, recently sat down for a great, relaxed, and open discussion with Dave DeWalt, the former CEO of FireEye and McAfee. As she astutely mentioned, cybersecurity has become a “kitchen table” discussion across America over the last year, […]
5 Steps to Stronger K-12 Chromebook Security
As a second installment related to October’s Cybersecurity Awareness Month, we wanted to highlight the fact that we’re two months into the new school year and focus on the mobile security implications of both the hybrid and in-person models that educational institutions are grappling with protecting. While so many educators, […]
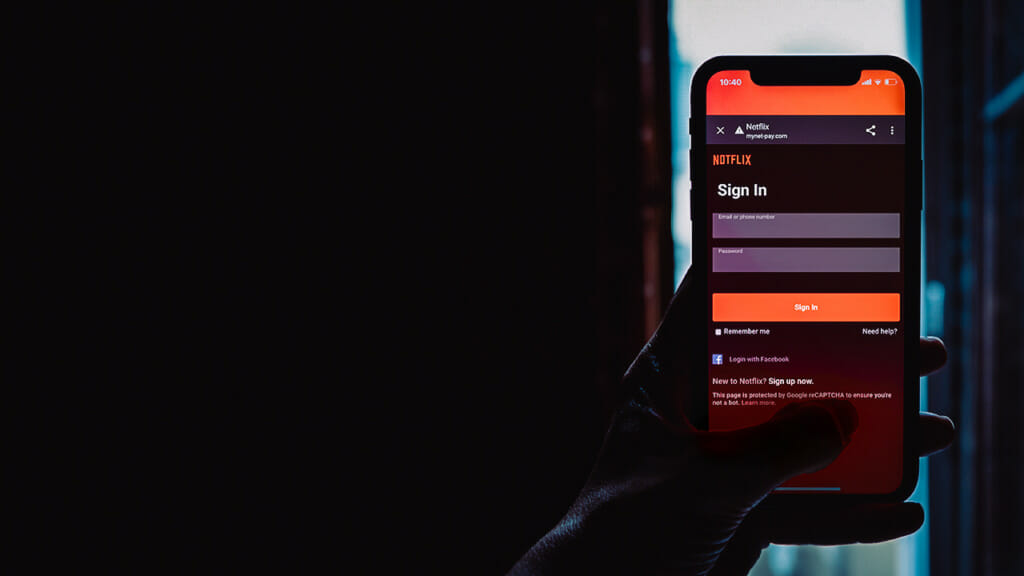
The Evolution of Mobile Specific Phishing
Over the last few months, the Zimperium zLabs team has been actively monitoring the rise in phishing attacks and some new data started to stand out. While phishing has predominantly been device-agnostic, meaning it did not rely on or change based on the operating system or device type, a trend […]
Pegasus Spyware Resurfaces with Newly Revealed Zero-Click Vulnerability
On September 13, The Citizen Lab revealed new research surrounding the Pegasus spyware campaign, presenting further details around their discovery of a zero-click vulnerability targeting Apple devices across the entire endpoint ecosystem. In response to the disclosure, Apple has released security updates for all their devices from mobile to desktop. […]