On February 26, 2018, we received a notification from the detection system about a malicious sample with a suspicious package and Play Store name. We quickly verified the automatic analysis and confirmed the sample was actively trying to scam users to download it instead of the original BBC News mobile app.
On February 26, 2018, we received a notification from the detection system about a malicious sample with a suspicious package and Play Store name. We quickly verified the automatic analysis and confirmed the sample was actively trying to scam users to download it instead of the original BBC News mobile app.
Fake BBC Metadata
- Application Name: BBC News
- Company Name: BBC Worldwide [Ltd] (the original uses round brackets)
- Package Name: in.com.bbc.mobile.news.ww
- SHA256: 6df385b3f26725ceb9530bd6422910ee8501cc2d03a6fa3b515a7ce658a8a4e5
- Download Link: https://play.google.com/store/apps/details?id=in.com.bbc.mobile.news.ww (which is now unavailable). A cached copy of the original Play Store page can be found here.
Behavioral analysis
Once installed the fake app looks exactly like the original, the icons and drawers labels are the same, but once opened we can spot several differences: On the fake application, we can identify that the BBC News page is loaded in a WebView and that Ads seems to be spawned while browsing the tabs or reading a news.

Fake BBC News app
Real BBC News app
Static analysis
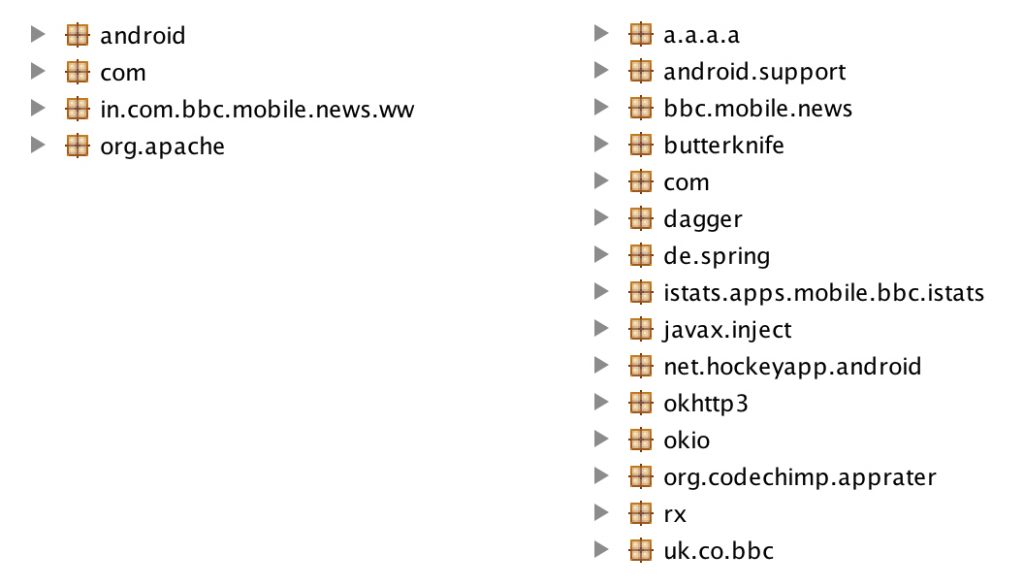
The application seems to have been around since June 21, 2017 and spread on all the unofficial Android markets and APK sites. Checking the AndroidManifest.xml, we can see that the versionName is 4.3.0.25, and comparing the fake and original samples from the same time period we notice a different package structure:
The fake package structure can be seen on the left and the real package structure can be seen on the right. The huge gap in the file sizes is also hinting that the differences are not limited to the Java code: 4 MB for the fake app and 15 MB for the original app. In fact all of the assets and resources do not match.
Usually the authors of such fake applications clone the original packages and inject some ads into them, but investigating the source code and the generated traffic from this sample we can notice that the fake application is acting as a placeholder. Its core structure could potentially be used to imitate other news mobile apps, or more generally mobile apps of services that also has a mobile website that can be loaded in the WebView.
Capturing the traffic, we noticed that the first query is sent to the malicious URL srv1.androidcreator.com; more specifically the following request took place:
The application sends several pieces of information to the server and amongst them we can identify the vname=4.3.0.25, idapp=273964 and pn=in.com.bbc.mobile.news.ww to identify the application; some information about the device environment and the idusu=229581196 which is referenced several times in the source code and seems to be uniquely identifying the owner of the device. After the query has been processed, the server answers back with a bunch of configurations that will be appropriately handled by the application:
We can spot several strings (some of them appeared also in the video): Rate our app, Do you like the app?, Yes, rate now, Maybe later, I recommend you this application for live tv, I am sending you this application that you may be interested.
The URLs to be loaded are present too: http://mobile.9apps.tv, http://www.bbc.com/news. We can also identify configurations about the UserAgent to be used or the title to be displayed. Finally, the advertisements IDs are received; this fake application is relying on AdMob and AppNext for the monetization process. Further analysis of the sample clarified that there is a core structure common to other samples too, and that it has been built by the Android Creator utility available at: www.androidcreator.com
A quick look into Android Creator
During the initialization phase, after the request and response with the server, the application checks if an updated version of the app is available and if available it will update. The response contains information about colors, labels and other graphical components to be used in the button or tabs of the app, confirming again that the concept is to have an application capable of adapting to several graphical layouts for maximal reuse. The utility lets the user build an application without actually knowing how to code for Android and all the configurations and actions are carried on using requests and responses between the application and the androidcreator.com server.
Querying Google we found several applications built with the utility, as an example the query “site:androidcreator.com” will return results for other applications and using the query “site:androidcreator.com BBC” will get the application ID of the Fake BBC app.
Banner of the Fake BBC News app in the androidcreator.com site.
We mentioned that the Android Creator utility let the user configure several actions, the Fake BBC News application contains the following request pages part of the srv1.androidcreator.com/srv/ URL, some examples are:
- cancelar_privado.php
- cancelar_solicitud.php
- chats_home.php
- coments_profile.php
- config.php
- eliminar_coment.php
- eliminar_fotogal.php
- eliminar_perfil.php
- eliminar_usu.php
- enviar_coment.php
- enviar_foto.php
- enviar_mensaje.php
- enviarmensaje.php
- favorito_usu.php
- fondo_guardado.php
- fotos_profile.php
Conclusion
The embedding of the ads seems to be optional, so we can surmise that the main goal of the Fake BBC News application seems to be monetization. The analyzed sample didn’t show dropping capabilities or sensitive data exfiltration, so it should be considered as an AdWare.
IOC
Fake BBC News: 6df385b3f26725ceb9530bd6422910ee8501cc2d03a6fa3b515a7ce658a8a4e5
Thanks
I would like to thank my fellow Zimperium teammates for their expertise and assistance, especially Gianluca Braga (@Matrix86_) and Christy Matthew (christypriory) .