Researchers: Ori Karliner (@oriHCX)
Researchers: Ori Karliner (@oriHCX)
Relevant Operating Systems: FreeRTOS up to V10.0.1 (with FreeRTOS+TCP), AWS FreeRTOS up to V1.3.1, WHIS OpenRTOS and SafeRTOS (With WHIS Connect middleware TCP/IP components) .
CVE List:
[wpsm_comparison_table id=”4″ class=””]
As a part of our ongoing IoT platform research, zLabs recently analyzed some of the leading operating systems in the IoT market, including FreeRTOS. FreeRTOS is a market leader in the IoT and embedded platforms market, being ported to over 40 hardware platforms over the last 14 years. In November 2017, Amazon Web Services (AWS) took stewardship for the FreeRTOS kernel and its components.
AWS FreeRTOS aims to provide a fully enabled IoT platform for microcontrollers, by bundling the FreeRTOS kernel together with the FreeRTOS TCP/IP stack, modules for secure connectivity, over the air updates, code signing, AWS cloud support, and more.
With the infrastructure that AWS provide, and the AWS FreeRTOS platform, developers can focus solely on innovation, thus reducing development time and costs.

There is also a commercial version of FreeRTOS, named OpenRTOS and maintained by WITTENSTEIN high integrity systems (WHIS). WHIS also offers a safety-oriented RTOS named SafeRTOS, that is based on the functional model of FreeRTOS, and is certified for use in safety critical systems.
FreeRTOS and SafeRTOS have been used in a wide variety of industries: IoT, Aerospace, Medical, Automotive, and more. Due to the high risk nature of devices in some of these industries, zLabs decided to take a look at the connectivity components that are paired with these OS’s. Clearly, devices that have connectivity to the outside world are at a higher degree of risk of being attacked.
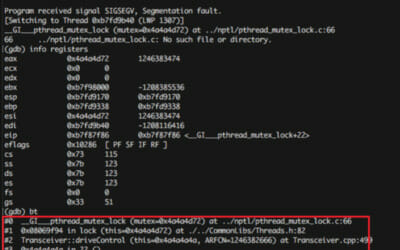
During our research, we discovered multiple vulnerabilities within FreeRTOS’s TCP/IP stack and in the AWS secure connectivity modules. The same vulnerabilities are present in WHIS Connect TCP/IP component for OpenRTOSSafeRTOS.
These vulnerabilities allow an attacker to crash the device, leak information from the device’s memory, and remotely execute code on it, thus completely compromising it.
We disclosed these vulnerabilities to Amazon, and collaborated (and continue to do so) with them to produce patches to the vulnerabilities we detected.
The patches were deployed for AWS FreeRTOS versions 1.3.2 and onwards. We also received confirmation from WHIS that they were exposed to the same vulnerabilities, and those were patched together with Amazon.
Since this is an open source project, we will wait for 30 days before publishing technical details about our findings, to allow smaller vendors to patch the vulnerabilities.
If you suspect that one or more of your products might be vulnerable and want our help with assessing the situation, please contact us at freertos@zimperium.com.