Integration extends Zimperium solution to include ZecOps’ automated agentless Digital Forensics and Incident Response (DFIR) capabilities Our new strategic partnership with ZecOps, the leading agentless automated Digital Forensics and Incident Response (DFIR) company, provides Zimperium customers with the only comprehensive mobile detection, forensics and incident response solution delivering the following […]
Resources
Addressing Critical iOS “Zero-Click” Mail Vulnerabilities
Recently, two vulnerabilities were disclosed in the default iOS Mail application that have existed since 2012 (iOS 6). According to the disclosing company, ZecOps, both vulnerabilities allow remote code execution capabilities and enable an attacker to remotely infect a device. ZecOps has also reported that both vulnerabilities were triggered in-the-wild […]
COVID-19 Threats Against Mobile Remote Workers: What Enterprises Need to Know
COVID-19 has created a situation unlike anything many of us have ever seen; yet one that will likely leave permanent changes in remote working. With the overnight tectonic shift towards entire workforces working remotely from home, on all variety of corporate and personal (bring your own) devices, IT and security […]
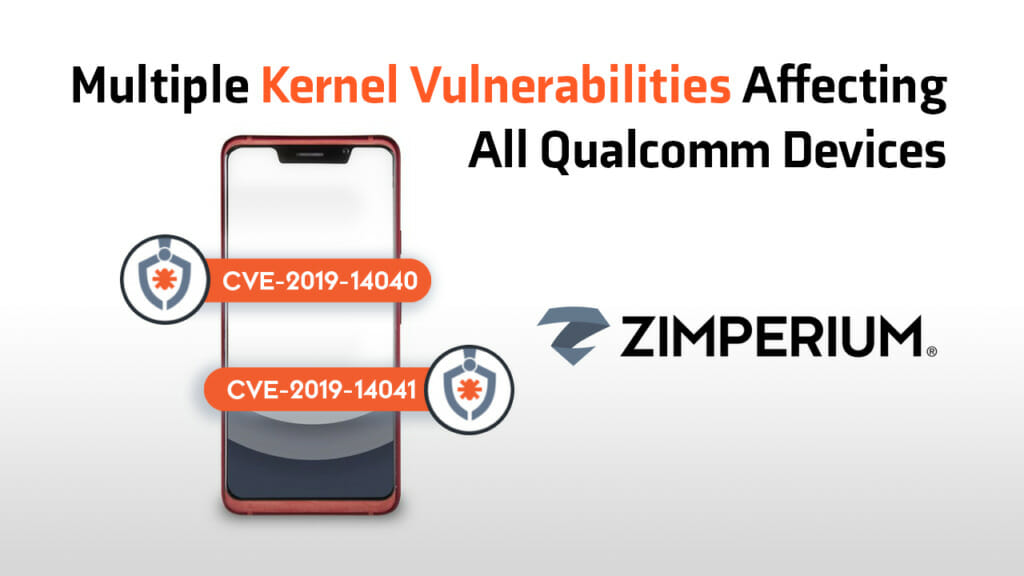
Multiple Kernel Vulnerabilities Affecting All Qualcomm Devices
Eight months ago, the Zimperium research team (zLabs) disclosed to Qualcomm two kernel vulnerabilities affecting all Android devices with Qualcomm chipsets. These vulnerabilities, combined with other vulnerabilities previously discovered by zLabs (CVE-2017-13253, CVE-2018-9411 and CVE-2018-9539) could allow a malicious app which was not given any permissions to achieve full root […]
3 Reasons Mobile App Security Should be a Top Priority
There is a reasonable chance you are reading this blog using an app on a mobile device. As of 2019, 53% of all internet traffic was from mobile devices such as smartphones and tablets (and growing). And if you are reading this on a smartphone app, then it’s a near-certainty […]
Enhance App Shielding with In-App Protection
Mobile devices and the apps operating on them expose your backend systems to cyberattacks. Attackers exploit vulnerabilities in mobile operating systems and in your apps to spy on your users, grab their private data, or even steal their money. In response, many mobile app developers are using app shielding, sometimes […]
Unified Endpoint Security with VMware & Zimperium
We have said this many times: an endpoint is an endpoint is an endpoint. Today, users perform more than 80% of their daily work on mobile devices. These devices contain or have access to the same information and applications traditional endpoints (laptop, desktop) do. Unfortunately, they also expose organizations to […]
A Deeper Dive into Phishing Attacks
written and researched by Nicolás Chiaraviglio and Santiago A. Rodriguez As mentioned in our blog post on mobile phishing, there are different types of phishing attacks. Here, we’ll dig deeper into the different types that exist. Moreover, we’ll take a look at phishing kits, a tool that allows non-technical scammers […]
Gone (Mobile) Phishing
written and researched by Nicolás Chiaraviglio and Santiago A. Rodriguez CISOs worldwide are scrambling to address phishing attacks. In the second quarter of 2019 alone, there were close to 130 million phishing attacks, taking place on different types of devices within an enterprise – – desktops, laptops and mobile devices. […]
Zimperium Extends Mobile Security Leadership by Delivering First Complete Mobile Application Security Solution
New Mobile Application Protection Suite (MAPS) Identifies Security, Privacy and Compliance Issues During Development and Protects Apps While In Use Mobile applications have become a business requirement for almost every organization. According to a recent report, four out of 10 large enterprises are planning to deliver more than 50 apps […]
Mobile Security Updates
Recent Posts
- What Good Mobile App Security Visibility Looks Like: Discover What Lurks Within Your Enterprise’s Mobile Ecosystem
- Zimperium Positioned as the Leader in the 2024 SPARK MatrixTM for In-App Protection by Quadrant Knowledge Solutions
- Understanding IRAP: Australia’s Commitment to Upholding Best-in-Class Security Standards