In the aftermath of Edward Snowden’s revelations about mass-surveillance by the U.S. government in 2013, technology companies have made a serious effort to convince their customers that they are in support of strong privacy by incorporating encryption policies.
 Popular messaging apps like Signal, WhatsApp and Telegram have added end-to-end encryption protocols, meaning only their users are able to view communications. Apple iPhones now have longer, more complex passwords linked to underlying encryption, making them harder to hack.
Popular messaging apps like Signal, WhatsApp and Telegram have added end-to-end encryption protocols, meaning only their users are able to view communications. Apple iPhones now have longer, more complex passwords linked to underlying encryption, making them harder to hack.
But encryption still doesn’t guarantee unbreakable security and, with enough resources, it can be bypassed. Take the CIA breach last week, where WikiLeaks published documents about the tools that the CIA has developed to hack smartphones and other Internet connected devices. By targeting these devices, the CIA is reportedly able to bypass encrypted-communications on popular apps like Signal and WhatsApp, proving that a cyber criminal could easily do the same. Here are three reasons why encryption isn’t enough to protect mobile devices:
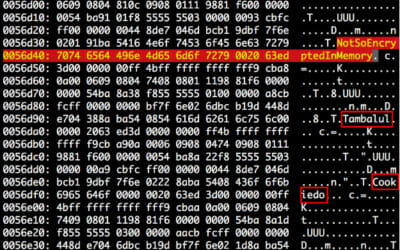
- Encryption isn’t foolproof: Encryption alone can’t stop a determined hacker from penetrating a mobile device — it’s just the first layer of technology they need to bypass in order to hit their target. For example, Telegram promoted its “Secret Chat” function as a way for users to send end-to-end encrypted messages. But by simulating an attack originating from an app/client side vulnerability that gains additional permissions by running a kernel or root exploit, Zimperium was able to uncover Secret Chats written in plain-text in the process memory. Not so safe after all.
- Mixed messages: While encryption made headlines during the Apple vs. FBI dispute, big companies like Facebook and Google have struggled to implement strong encryption policies without impacting their business objectives. Facebook received backlash from consumers after announcing that its Messenger application will offer encryption as an opt-in option because making it a default feature would interrupt the new machine learning components of the app. Google also released messaging app called Allo that offered encryption as an opt-in feature. While both companies are offering encryption as a security option, it’s up to users to turn on the feature within the app for extra privacy.
- Don’t believe the hype: While encryption is a critical component of security, it’s not enough to protect mobile devices. As companies continue to develop new technologies, new risks are being exposed and cyber criminals are becoming even more sophisticated. Not to mention, live data, or the type of information users interact with directly, is never encrypted and is an easy target for attackers. Unless users are detecting this type of threat via intrusions on their device, network or applications then they are susceptible to attacks.
Encryption shouldn’t be relied upon as the be-all and end-all security approach. It’s time to stop fixating on encryption as the “go-to technology” and instead implement a Mobile Threat Defense platform to protect employees, partners and customers from the next generation of threats.
Read the full version of this article in Wireless Week’s CTIA Show Dailies here (pg. 8).