Triada, a modular, stealthy and persistent Trojan targeting Android devices, was recently seen in the wild and reported on March 3, 2016. It, like so many others that we see daily, actively uses root privileges and operates silently to take over a device. Triada is primarily propagated through malicious applications that users download/install from untrusted sources. Originally, these malicious applications obtained unauthorized super-user privileges to install legitimate apps and display advertising. Now these same advertising botnets, Leech, Ztorg and Gorpo, are installing Triada too.
Triada contains modular functionality and after getting into a user’s device, it injects itself in nearly every working process and continues to exist in memory. Triada uses the Zygote system process to inject itself into other system processes. Since Zygote’s purpose is to launch Android applications, Triada becomes part of any launched application by Zygote and can, in turn, modify the application’s operation to any desired outcome by the malware authors. All of the running Trojan processes are hidden from the user and other applications. As a result, it is difficult for both the user and antivirus solutions to detect and remove Triada.
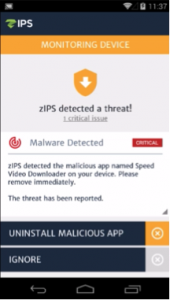 Zimperium’s z9 engine detected Triada without any updates. In fact, after taking a deeper dive, we find that we detected Triada as early as May 2, 2015 and have seen this malware in the US, Yemen, Turkey, the West Bank and Germany. z9 was explicitly designed to protect against sophisticated classes of attacks including those used by this type of malware. zIPS, our on-device mobile threat protection app, notifies the user of the malicious app, and displays a warning and an automatic option to remove the malware at three critical stages: download of the malware sample, installation of the sample and finally at runtime. Full forensics for the affected files, C&C communications and what modifications the malware was able to perform are provided.
Zimperium’s z9 engine detected Triada without any updates. In fact, after taking a deeper dive, we find that we detected Triada as early as May 2, 2015 and have seen this malware in the US, Yemen, Turkey, the West Bank and Germany. z9 was explicitly designed to protect against sophisticated classes of attacks including those used by this type of malware. zIPS, our on-device mobile threat protection app, notifies the user of the malicious app, and displays a warning and an automatic option to remove the malware at three critical stages: download of the malware sample, installation of the sample and finally at runtime. Full forensics for the affected files, C&C communications and what modifications the malware was able to perform are provided.
While we see a large amount of rooting malware every day and consider the rooting capability a basic capability for malware, Triada’s other attributes are indications of cybercriminals stepping up their game. It should be noted that Triada affects users of Android 4.4.4 and earlier. If a system upgrade is an option, it would definitely be in order.