 Your million dollar 0day just got burned and now worth nothing? No worries – we are still interested in your exploit. The value of 0days can range from a few thousands to even a million dollars for a full remote exploit chain and many companies and governments are willing to buy them. The problem with this approach is your exploits are used for attacks against unknown targets (security researchers, press reporters and activists are all well known targets). As soon as the vulnerability is discovered and patched, sophisticated attackers will stop exploiting this bug and it is rendered useless. Professional hackers-for-hire try not to rely on N days to avoid getting caught.
Your million dollar 0day just got burned and now worth nothing? No worries – we are still interested in your exploit. The value of 0days can range from a few thousands to even a million dollars for a full remote exploit chain and many companies and governments are willing to buy them. The problem with this approach is your exploits are used for attacks against unknown targets (security researchers, press reporters and activists are all well known targets). As soon as the vulnerability is discovered and patched, sophisticated attackers will stop exploiting this bug and it is rendered useless. Professional hackers-for-hire try not to rely on N days to avoid getting caught.
In many cases, exploit buyers will not pay the full exploit price in case the vulnerability gets fixed by the vendor.
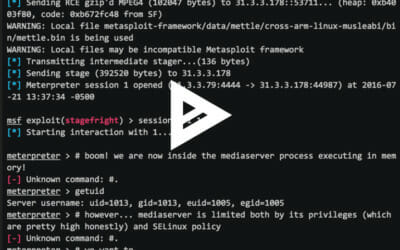
How much is an 0day worth in the latest Android or iOS? Possibly even a million dollars for a remote, generic, exploit. How much is the same 0day worth one month after the bug was patched? Sometimes as low as zero dollars. In our efforts to promote patching in mobile devices, we seek to change this process and help companies and researchers alike. We now offer a purchasing program for N-Days exploits.
It’s simple. We’ll buy remote or local exploits targeting any version other than the latest version of iOS and Android.
The exploit will be released first to Zimperium Handset Alliance (ZHA) partners. ZHA includes 30+ of the most well-known carriers and handset vendors. Amongst our ZHA partners you can find: Samsung, Softbank, Telstra and Blackberry. The complete list is available only to the security contacts within the carriers and vendors.
We will provide ZHA partners between one to three months advanced notice, before releasing the exploit publicly (unlike most exploit acquisition programs). We will not release these exploits publicly if requested by the author. We would like to encourage security researchers to provide proofs for exploitation of known vulnerabilities and at the same time, getting paid for previous work. Multiple ZHA partners explained to us that without proof of exploitability, it’s hard to convince the security teams to allocate resources needed for a complete patch cycle, even for known issues. We hope this program will encourage more researchers to look into monthly security updates, and promote better patching.
FAQ
What will Zimperium do with the exploits?
Our plan is to use the exploits to enhance our z9 engine. So far, all of the publicly available kernel exploits released over the last few years were detected by our z9 engine, without requiring an update. As a mobile security vendor, it is obvious that we should support the latest devices – but on large deployments, and tens of millions of users – we must also provide backward compatibility and identify attacks on devices that even the device vendors are no longer supporting anymore (e.g: Android 4.1). In such scenarios, the users do not even have the option to update their phone. For us, supporting old devices is a key decision to help where the update policy have failed the consumers.
Why are you buying N-days?
Security research and exploitation is in our heart and what led Zimperium to this point. We appreciate the art of exploitation, and appreciate cool tricks in order to write an exploit development, bypass ASLR/KASLR, achieve persistency, etc. We humbly believe that we can learn from any exploit and as a result offer better security for our customers and partners.
Are you planning to buy 0days, too?
No.
Will you release the exploit?
Yes, unless explicitly asked by the author. Our goal is to help the community, penetration testers, mobility and IT Admins to better evaluate their security and protect their devices.
Will you provide credit for the exploit developer?
Yes, unless asked to remain anonymous.
What are the payment methods?
We can do an electronic transfer or PayPal.
How much is going to be allocated for the Zimperium N-Days EAP?
We will allocate 1.5 million US dollars for this program.
How will you decide which exploit gets purchased and for how much?
An exploit committee built from selected members of zLabs will decide how much to offer for each N-Day exploit. Remote exploits are valuable even more than local ones, but it all depends on the exact bug (and the beauty of the exploit).
What type of bugs are we looking for?
- Remote exploits
- Local exploits
- Information disclosure vulnerabilities
- Other vulnerabilities can apply but needed to be described in the email
How does it work?
Send us a note to ninja_exploits@nothuman.ninja (PGP key below).
- Describe the exploit
- When was it patched? (which CVE)
- How does the exploit chain work?
- Do you want to release the code publicly after we check it in our labs? if so, would you like to receive credit for it? If (4) is not provided, the default is yes.
We will then verify your submission and provide you with a quote containing our offer. Once you agree to the terms, we will submit the payment.
ninja_exploits@nothuman.ninja – public key
—–BEGIN PGP PUBLIC KEY BLOCK—–
mQINBFiQqC0BEADK4nKmyh+mWMXNeQOM+2Ch2RyRgOkd4rJUgMA+0PbyPMWGsdPA
Ys74j4zJq2SjmK/mEvi8z3uSCq1e9bfH1qSNWsqkm/fa+00iryWv/VaqHeEDrOIW
RdwOPrnPLxjeBCHHtaCWPrfKXtZB7DG+abC4R8jsJ3BZ9kih9PQWXnLdM90gGbNp
JSCLEaVcC9WoiamRex9TasSo1J9auGmttcktlBdKusYkzYIQUH7V5b8gseunn8xz
W9fMGWlwk3gu0MV4iJ8Z666NbQFQWdRCabpEb+kj3R39p12mhvtrtru1bQrswX+v
qfYfFZscJ0CFFVRin2naAapNxJ393rmKA/NtVDsBZPmN3WFUy9twTxFXsy0OvDxQ
Rrl4SvMg/Em84noDHndPSmNf0cG6dTEt3CkYHANys0ucir44qFHIxV3GqVMOgqyR
CwcXg2YJePPcblJz70+fBst4y2W7iE0ocU1rqr646EP16wnh/KSJGJtgzccoSwpJ
SvoqYmoU7nYRgF4dzvjJwG+8cuXQI5Pz7dvUJXg8N7FDE3XR4L9Zw8u0vtuloTsp
FUsXjm157Tl5bg0scbJp0CRNFSKVL99mYGLcH5rCaphwpmOu9X3raC2ZCQQZP1IR
WZB6NltrCpYfmxqUnU1WXmjDkvg/pVphXY39MrhbZpFyxbh6htWVvFa9iwARAQAB
tC5OaW5qYSBFeHBsb2l0cyA8bmluamFfZXhwbG9pdHNAbm90aHVtYW4ubmluamE+
iQI9BBMBCgAnBQJYkKgtAhsDBQkHhh+ABQsJCAcDBRUKCQgLBRYCAwEAAh4BAheA
AAoJEFXz+k0u4hSmURsP/3eB9vf2vPQNr2sXq2m2NSOhp6FYBO6w8BTwirZsTUxz
glROPNNKP2hr7IntP+OVlDN1lF5MWjliqsNSXnJSuD9DF+UbGrLGHSk48emBwC2D
OdHGQUvErhYQ6/ptmJTmEN1CWrhM0BWaut6druxpQ8QO7E9fUHptiFAgk8L5xzDZ
8Wmzzssd3VEtn7UHymh/+7wExmu5xMHzQXEpqw528aeJ0c87MioJvIL5hWAUbLU1
gXee721ZpE+tZzY0nkE/RGMLUL5iVMOPx+8qGXFC1B6zsDhp/m0yh1SR27Kon1ia
Fw+mNW3Jf1UoWoxiyTsLlTdaOTwOg5EnosehgA8XzXoE9JB+tA30XQnp+SV+b2NB
AzHTnx+aMSit2UM5R9f4R2WhT9UGpPkQyKGXUgqSh2T9Um24mk1pL0/BMPy9GpxD
pYx956edlCpdhvJgGyvwEA4qcGf3h2fAfxb7373L112H8kkGRPNt8ghiFZawbzGY
4WwP9EXIvYhXLnk1OQf+HcoMTNf1c/6PUlr4EjIZwluC/yvOjS0iDiBxVWSDDzUB
IXUJnoVJeKGC3BXqjxVX2LgwQxfziUOi57xW5pnL/Q9C3FdB57pnYkCr2wn/OZNJ
jZQyVr5Vj2jHjkHEZ/FrYvHqoNI2wHtSVG6exSutkwlLFikPb9RAGBTKnkhNrumZ
uQINBFiQqC0BEACuXXpr88/DZ9kN4aTyyO7VegQxVHbteh1x7hBehICPmDkHDkTy
o1arMPRuIk5ycOZj/IUMuZsSRBbRupjSp9Apr0TQXPFnYwAQ/wty0KeEgFFHNgVN
TPLdLbfschxEl3J9P7/Iz79n1z2z9OWV5vQ6zRMSlLOmO3NMM2VR0cu3R8V9dV4q
m/JhG2yaAEKl4R81LTCuQuYXy8FvpA+sNXgUpjgw9rkZLvMBu3dCRbZ0NsKF5/W0
xoFoCp9Y/0qF6xBQ5BbzZ0WRdZh9JYQcfTIzxaNYbkX3ig0usxqqB/Wm/9c088hg
JD+hk6qxHuuwNd/H3vFjVySHYtcJRXZ4g+EhXf0SSmKN64tOGJCqhMU4pmMZu2mY
/nSVS+KzoSxSjTnVmLCLRF0u3Q7YoDicCyc2oRvvpvqnMJ2N88waKVd5gvLSZdGg
b4ninzCwUmtKIazSaIA8JAtZn2n5r4FI7/5RKgNuINDAkgwpEBdCHwV1Tsoma3uN
oy89mxR2/Pu8BEAH9SVvG38wgyi/dWjJK2YLhT4YIRu/47xPl0y1PHsW3ZHUC9cw
jEAFVZ2WyCaypOjprgiiqoNoeZl+m0ePuHXu/+m1rqUrTq95oq/DdmuhqAwXSq8V
yodKnrFZ8JnjDJlEOMGIzz8mM/b1dWI5qrjH+4tUXhkDbJJQeNSGiAe+EQARAQAB
iQIlBBgBCgAPBQJYkKgtAhsMBQkHhh+AAAoJEFXz+k0u4hSmaJ0P+wY13QDNTawv
qmX8P+fYjz1W2p5NJekJ7DxXOvBNxpvBtpAie7zf7qQgkDjB+mtbv3bo+CSQiCBX
KIgd+GPmZbTkmI4sszvse95zHKuXRZ40eAgQdATmKGsTObuc4Uv1OjorOPg8/rKM
brSwwJZ41fb2HFRSFN/l4UOuvTCypn+p0GwN2VjE865PhnxN2J2UcxJ9SRa4J9nA
z8eVJU8SyOo7867Q4DcATX/dC1HQH+DWSm9DadaNqia+Jd7NDn7aRFqxtPtHegiB
GBkCwM/njBObhMaBMdXe1Dc+k9ZFwZFio3KwofwlDGiMtFFetQ5G+Wym5F1FChug
9FlH7DXsVkWK4DDpuhWNwErhxTMDF82S0T/rDTkefLn1zGGreZSb4LOmsCgz949Q
5XUyPOjaiiDAIUwBwH0guCnazgOX/ER+SyczlkOuXNIbweQQ5A02PWu2L9rfIGfK
KLIn6dzVtVwPQSOwmMhIsZJ6gLcHQJo7RDpA6o4g/AQzqHI9/H6rbl2caXW6039F
6NlHwgBOkAtsWe2sHQsm2FpZPAi3sNvfRii53YZItrnNzPqto7/DlEYM56g/+jS3
UEjOE/fO0tzewYEdpf59awvTJpoQ/qg+657jEMiJv7pcX4nezTRBw5GYQLUPhFhw
FxXTstmdyCSLg4pgi1dfg9rRimmYcHmL
=8JuZ
—–END PGP PUBLIC KEY BLOCK—–